Published on
Invalid Date
The attack surface for malicious actors has grown exponentially. In 2024 alone, reported cybercrime losses exceeded $16 billion in the U.S., driven largely by exploitation and ransomware targeting connected systems.
Concurrently, software supply chain failures have become a critical global risk, with high-risk vulnerabilities spiking 36% year-over-year. To combat this systemic vulnerability, the European Union has enacted the Cyber Resilience Act (CRA), a landmark regulation establishing a unified, mandatory cybersecurity framework for the entire product lifecycle.
About the Cyber Resilience Act (CRA)
The fundamental paradigm shift introduced by the CRA is the legal transfer of cybersecurity responsibility away from the end-user and directly onto the economic operators : manufacturers, importers, and distributors. The regulation mandates that these entities:
- Embed security by design, meaning cybersecurity must be integrated into every phase of a product's lifecycle. Manufacturers cannot legally ship products with known exploitable vulnerabilities and must enforce a "secure by default" configuration.
- Conduct conformity assessments. Before placing a product on the EU market, manufacturers must formally assess and document compliance, resulting in the application of a CE mark.
- Execute rapid vulnerability remediation by actively monitoring for, report, and patch vulnerabilities and severe incidents throughout the product's defined support period.
The financial penalties for failing to meet these obligations are severe. Violations of core cybersecurity requirements or reporting mandates can trigger administrative fines of up to €15 million or 2.5% of the organization's global annual turnover, whichever is higher. Furthermore, market surveillance authorities possess the power to order mandatory product recalls or completely ban non-compliant products from the European market.
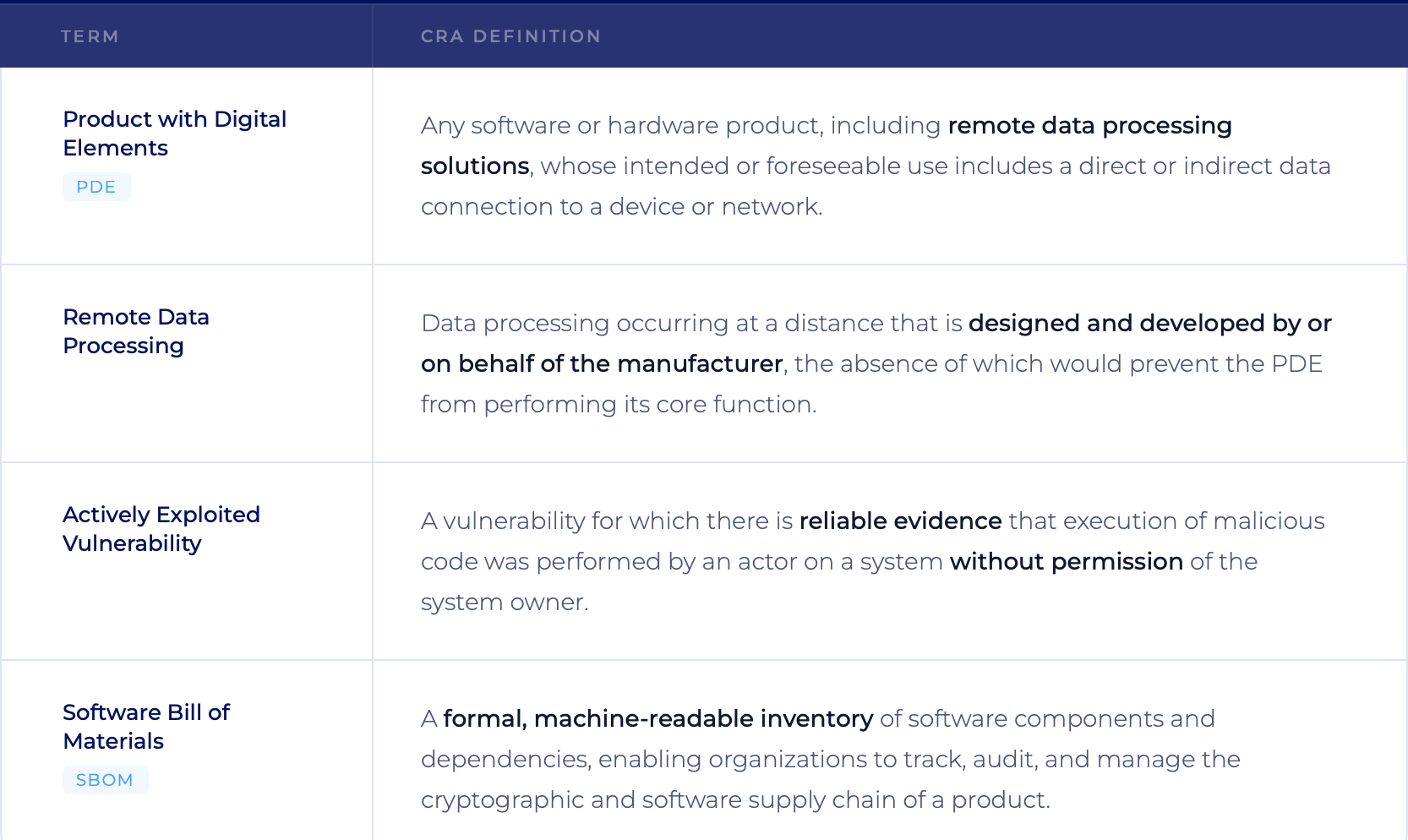
Essential definitions
Scope of application
The jurisdictional reach of the CRA is intentionally expansive and highly consequential for global infrastructure design.
Product scope
The CRA applies to almost any connected hardware or software distributed commercially within the EU. However, its inclusion of "remote data processing solutions" dramatically widens the net.
Consider a manufacturer producing connected industrial sensors. Not only must the physical sensor hardware and embedded firmware comply with the CRA, but the cloud-based dashboard and API backend required to configure and monitor those sensors are also fully in scope. Websites that merely provide marketing information are exempt, but backend cloud services essential to a device's operation are strictly regulated.
Exceptions are narrow and generally limited to sectors already governed by stringent safety regulations, such as medical devices, aviation, and national defense products.
Operational scope
The regulation applies to "economic operators" placing products on the market, regardless of where those entities are headquartered.
This means a software provider based in the United States or an electronics manufacturer in Asia must achieve full compliance if their products are utilized within the European Economic Area (EEA).
Importers and distributors share the burden; they are legally required to verify that the manufacturer has completed the necessary conformity assessments and applied the CE mark before facilitating the sale.
Implementation timeline
The CRA officially entered into force on December 10, 2024, initiating a phased transition period. Infrastructure leaders must align their product development roadmaps with the following critical enforcement dates:
Discover more articles
Explore our comprehensive collection of articles on various topics.
Browse Articles
- Early 2026: The European Commission will release official implementation guidance.
- June 11, 2026: Provisions governing the notification and operation of Conformity Assessment Bodies take effect.
- September 11, 2026: Immediate Enforcement of Article 14. Mandatory reporting obligations for actively exploited vulnerabilities and severe incidents go live via the ENISA Single Reporting Platform.
- December 11, 2027: Full CRA enforcement. All covered products must demonstrate verifiable compliance and bear the CE mark to enter or remain on the EU market.
The Reporting Crucible: Article 14 Deadlines
The most immediate operational challenge for CISOs is the September 11, 2026, activation of Article 14 reporting requirements. These apply to all in-scope products, including those already on the market. When a manufacturer discovers an actively exploited vulnerability or a severe security incident, they must notify their national Computer Security Incident Response Team (CSIRT) and ENISA through a centralized portal.
The required cadence is extremely aggressive and requires highly automated incident response workflows:
- Within 24 hours: submit an early warning notification detailing the affected product and known impacted territories.
- Within 72 hours: provide vulnerability notification, including the nature of the exploit and immediate mitigating actions.
- Within 14 days: deliver a final, detailed report confirming the deployment of a definitive corrective measure or patch.
The convergence of crises: Shorter certificate lifespans
Complicating the CRA's mandate for continuous, secure connectivity is a massive shift in foundational web security. The CA/Browser Forum has mandated a radical reduction in public TLS certificate lifespans.
- March 15, 2026 (soon) : Maximum validity drops to 200 days.
- March 15, 2027: Maximum validity drops to 100 days.
- March 15, 2029: Maximum validity collapses to just 47 days.
The CRA demands that remote devices "phone home" regularly for critical security updates. If an organization relies on manual spreadsheet tracking, the shift to 47-day renewals guarantees human error. An expired backend TLS certificate severs the connection to the field device, causing an immediate outage.
The financial stakes are staggering; analysts estimate that a severe certificate outage can cost modern enterprises up to $15 million per event, or $5,600 to $16,670 per minute of downtime. Manual certificate management is fundamentally incompatible with the uptime and automated patching requirements of the CRA.
How to ensure compliance ?
To meet the 2026 and 2027 deadlines, engineering and infrastructure teams should transition from reactive security to cryptographically enforced, continuous compliance.
1. Establish continuous cryptographic inventories
That includes identifying all cryptographic assets, from web server TLS certificates to embedded IoT keys. Given the impending 47-day certificate reality, manual tracking can be replaced with automated Certificate Lifecycle Management (CLM) platforms capable of continuous discovery, automated renewal, and real-time revocation.
2. Audit the Software Supply Chain and generate actionable SBOMs
The CRA requires the creation and maintenance of a machine-readable SBOM. However, generating a static list is insufficient. Emerging standards aligned with the CRA, such as Germany's BSI TR-03183-2, explicitly require that SBOMs be secured with cryptographic checksums and digital signatures to prove data integrity.
3. Operationalize the 14-say remediation window
Security teams must design and stress-test incident response pipelines capable of meeting the 24-hour, 72-hour, and 14-day ENISA reporting timelines. This requires deep integration between threat intelligence, CI/CD pipelines, and device management platforms to quickly isolate compromised systems and push fixes.
Fulfilling CRA mandates with PKI and CLM
While the CRA is technology-neutral, engineering a solution that satisfies its rigorous essential requirements relies heavily on a robust, highly automated Public Key Infrastructure.
- Enforcing secure authentication (Requirement I2d):
The CRA requires the elimination of default passwords and mandates robust access controls. By injecting a unique Initial Device Identity (IDevID) certificate into a hardware Root of Trust (like a TPM or Secure Element) during manufacturing, devices achieve cryptographically secure, certificate-backed authentication from the moment they power on.
- Securing data in transit (Requirement I2e):
The regulation demands state-of-the-art encryption for data transmission. A dynamic, automated PKI ensures all device-to-cloud communications utilize heavily authenticated TLS 1.3 or secure MQTT protocols, preventing interception.
- Guaranteeing update integrity (Requirement II7):
The CRA mandates mechanisms to securely distribute vulnerability patches. This necessitates strict, policy-driven code signing. By digitally signing all firmware updates and validating those signatures on the device before execution, manufacturers prevent malicious actors from hijacking the update mechanism to inject malware.
- Rapid incident mitigation:
In the event of a severe compromise requiring a 14-day ENISA resolution, an automated Certificate Lifecycle Management (CLM) platform enables administrators to instantly locate and revoke the certificates of compromised devices, cutting off their access to the enterprise network, while seamlessly deploying newly signed updates to secure the rest of the fleet.
Conclusion
The Cyber Resilience Act permanently alters the economics and engineering of digital products. Security can no longer be bolted on at the end of a development cycle; it must be cryptographically verifiable from design through decommissioning.
By utilizing mature Public Key Infrastructure, automated code signing, and enterprise-grade Certificate Lifecycle Management, organizations can meet the CRA’s demanding requirements for identity, integrity, and rapid vulnerability response. Transitioning to these automated frameworks not only secures compliance and prevents devastating fines, but it also transforms organizational resilience into a distinct competitive advantage in a heavily regulated global market.